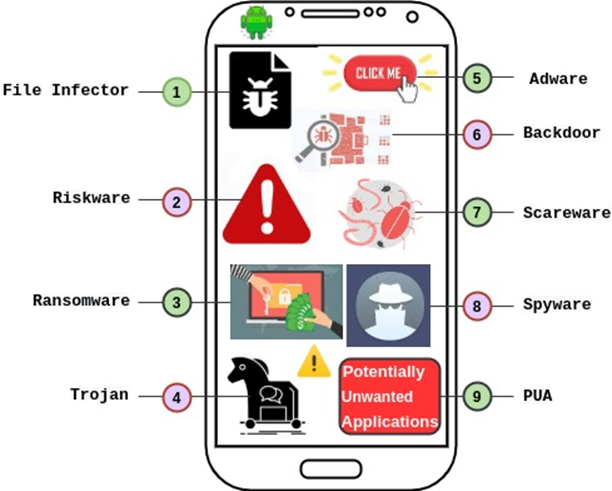
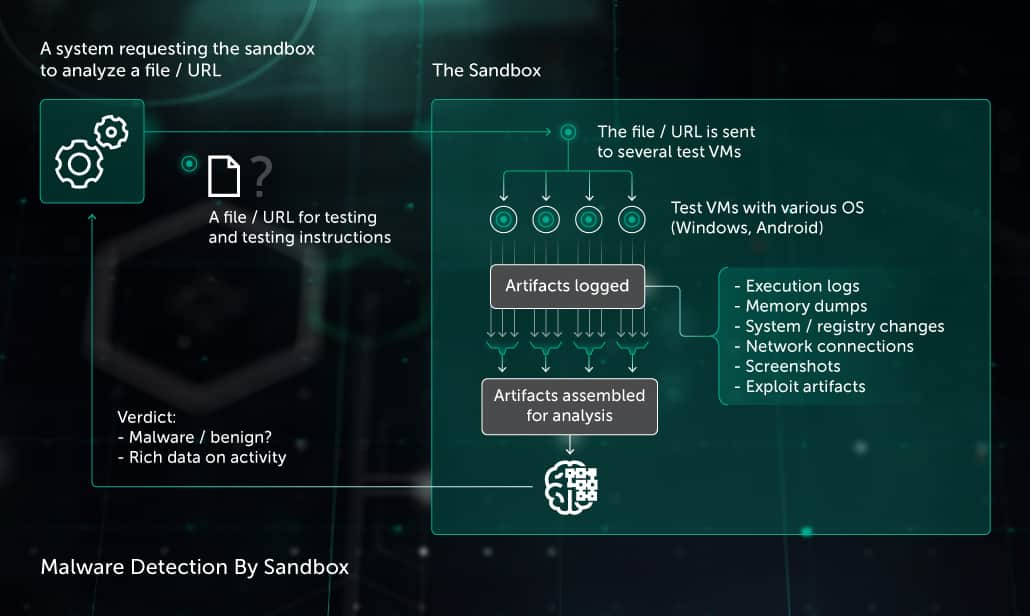
View of A Review on Android Malware: Attacks, Countermeasures and Challenges Ahead | Journal of Cyber Security and Mobility
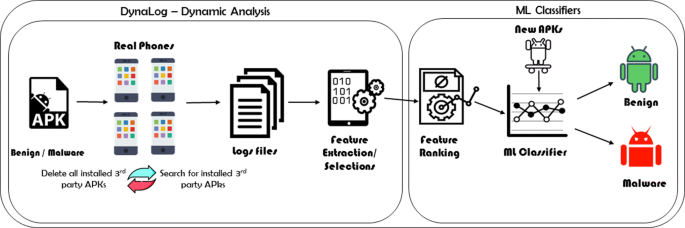
Machine learning-based dynamic analysis of Android apps with improved code coverage | EURASIP Journal on Information Security | Full Text
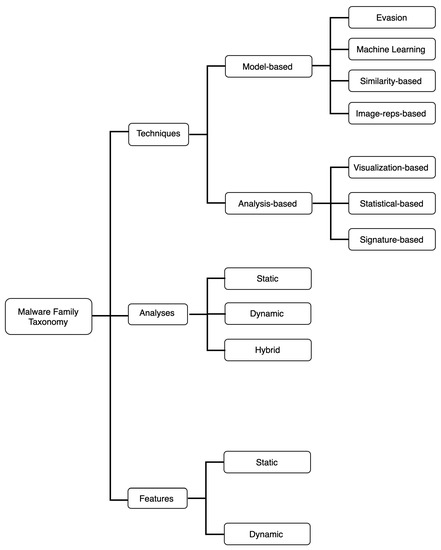
Electronics | Free Full-Text | Android Malware Family Classification and Analysis: Current Status and Future Directions | HTML